
This post contains affiliate links. If you buy through them, we may earn a small commission at no extra cost to you — thanks for supporting. Learn more.
1. AI-Powered VPNs at a Glance — Quick Verdict for Privacy-Focused Users
We’ve all had that moment: you connect to public Wi-Fi at a café, airport, or hotel… and a small voice in your head wonders, “Is this actually safe?”
You’re not imagining it. Online threats really are getting smarter — and faster. In fact, global cyberattacks rose 30% year-over-year, reaching over 1,600 attacks per organization per week in recent research (source here).
And it’s not slowing down. Another report shows more than 7.5 million cyber incidents recorded in 2025 alone, with mobile attacks rising 22% globally (source here).
Even more concerning: attackers are now using artificial intelligence themselves to automate and scale attacks, making them harder to detect and faster to execute.
Quick Verdict
If you care about privacy, public Wi-Fi safety, or protecting accounts and data, AI-powered VPNs are quickly becoming one of the smartest tools we can use today. They don’t just hide your connection — they actively analyze threats and adapt in real time.
Why this guide matters
Most VPN guides online focus only on speed or price. What we really need to understand is:
• how modern threats actually work and why AI-powered VPNs are built to detect them faster
• why traditional VPN protection isn’t always enough without real AI VPN security layers
• how AI is quietly changing digital security and redefining AI cybersecurity privacy
That’s exactly what we’ll break down here — simply and clearly.
At-a-glance comparison
| Protection Type | Traditional VPN | AI-Enhanced VPN |
|---|---|---|
| Threat detection | Static rules | Real-time adaptive analysis |
| Attack response | Manual or delayed | Automated blocking |
| Smart routing | Fixed servers | Optimized dynamically |
| Risk awareness | None | Predictive alerts |

all-in-one AI tools shows how automation and intelligence layers are becoming standard across modern platforms.
For a deeper look at the current threat landscape, this recent industry report summary explains why attacks are rising globally and why defensive AI is becoming essential: cyberattack growth statistics.

2. Why AI-Enhanced VPN Security Is Exploding in 2026 (Trends + Real Threat Data)
We’ve all noticed it lately: more password alerts, more suspicious emails, more “unusual login detected” notifications. It’s not just our imagination — the threat landscape really has changed, and it’s changing fast.
Recent cybersecurity reports show attacks are scaling at a speed traditional defenses struggle to match. In 2025 alone, AI-powered cyberattacks jumped 72% year-over-year, while automated scans reached 36,000 attempts per second globally (source here).
And it’s not just volume — it’s sophistication. Nearly 83% of phishing emails now use AI, making them more convincing and personalized than ever.
The shift happening right now
Security researchers are seeing a clear pattern:
| Trend | What’s Changing | Why It Matters |
|---|---|---|
| Attack speed | Breaches now happen in minutes | Humans can’t react fast enough |
| Automation | AI tools generate attacks | Lower barrier for hackers |
| Realism | Deepfakes + voice cloning rising | Harder to detect scams |
| Scale | ~1,925 attacks per organization weekly | No one is “too small” to target |
That last stat is especially important: organizations faced 1,925 attacks per week on average in early 2025, a 47% increase from the previous year.
Why this matters for everyday users
We often think cyberattacks target only big companies — but most attacks actually start with regular users, which is why VPN with AI protection tools are becoming essential:
• stolen credentials
• fake login pages
• compromised Wi-Fi
• browser exploits
Security analysts found 65% of intrusions start with social engineering, not software hacks — one reason AI-powered VPNs are designed to detect suspicious behavior earlier.
That means attackers don’t break systems first.
They trick people first — which is exactly where AI VPN security makes the biggest difference.
Where AI changes the game
Artificial intelligence isn’t just being used to build tools — it’s being used to run attacks. Malware can now adapt automatically, phishing messages mimic writing style, and some breaches even run without human intervention after launch.
That’s exactly why defensive tools are evolving too. Modern security platforms — including advanced privacy tools — now rely on automation and machine learning to detect patterns humans would miss.
If you wish to add an extra layer of protection you can see our tools we recommend in the post AI Privacy Gadgets here.
Why searches are spiking:
People aren’t suddenly curious about VPNs for no reason. They’re reacting to a real shift — threats are getting smarter, faster, and harder to spot.
And when attackers use AI…
we need protection that can keep up.
3. What an AI-Powered VPN Actually Does Differently (Features That Matter)

Most of us assume a VPN simply hides our IP address and that’s it. And honestly, that used to be true. Traditional VPNs were built mainly for encryption — like putting your data inside a sealed tunnel.
But today’s threats don’t just try to see your data. They try to analyze behavior, mimic users, and adapt in real time. That’s where AI-powered VPNs and modern AI VPN security systems start to work differently.
According to IBM’s security research, modern AI-driven defense systems can detect anomalies and suspicious patterns far faster than rule-based tools because they continuously learn from traffic behavior — which shows exactly how AI improves VPNs and strengthens real-world protection.
What changes with smarter protection
Instead of waiting for a threat signature, intelligent privacy tools monitor patterns such as:
unusual login timing
abnormal traffic routes
suspicious domain requests
behavioral deviations
This means protection shifts from:
“block known threats” → to → “predict and stop suspicious activity”
Key feature differences that actually matter
| Feature | Standard VPN | AI-Enhanced Protection |
|---|---|---|
| Threat detection | Signature-based | Behavior-based learning |
| Response speed | Delayed | Instant automated reaction |
| Server routing | Manual selection | Smart adaptive routing |
| Threat awareness | Static protection | Predictive monitoring |
We don’t experience cyber threats as technical events. We experience them as:
hacked accounts
strange login alerts
locked profiles
stolen subscriptions
Smarter protection tools reduce those risks before they escalate.
If you’ve seen how automation is transforming other digital tools, the same pattern applies here. Our guide on offline AI tools explains how intelligent systems increasingly run tasks silently in the background — security software included.
Simple takeaway:
The real difference isn’t just encryption anymore.
It’s awareness.
Traditional VPNs hide you.
Smarter ones watch for danger while you browse.
4. Best AI VPN Features to Look For Before Choosing One (Buyer-Style Guide)
You open a comparison page, see dozens of VPNs claiming to be the fastest, safest, most private… and they all sound identical. That’s exactly why choosing one can feel confusing — especially when many now advertise themselves as AI-powered VPNs without explaining what that really means.
The reality is simple: not every service labeled “smart” or “AI-enhanced” actually provides meaningful protection. What matters is which features genuinely improve security, how strong the AI VPN security system really is, and whether the platform delivers real AI cybersecurity privacy, not marketing buzzwords.
The features that actually make a difference
| Feature | Why It Matters | Look For This |
|---|---|---|
| Behavior monitoring | Detects suspicious activity early | Real-time alerts + automatic blocking |
| Smart routing | Avoids slow or unsafe servers | Auto-optimized server selection |
| Threat prediction | Stops attacks before they happen | Machine-learning detection engine |
| Kill switch automation | Prevents data leaks instantly | Instant disconnect on risk detection |
| Privacy transparency | Ensures no hidden tracking | Independent audit reports |
Quick checklist before you choose
Use this simple decision filter:




Security experts consistently recommend choosing providers that publish third-party audits and transparent infrastructure reports, since these verify privacy claims independently.
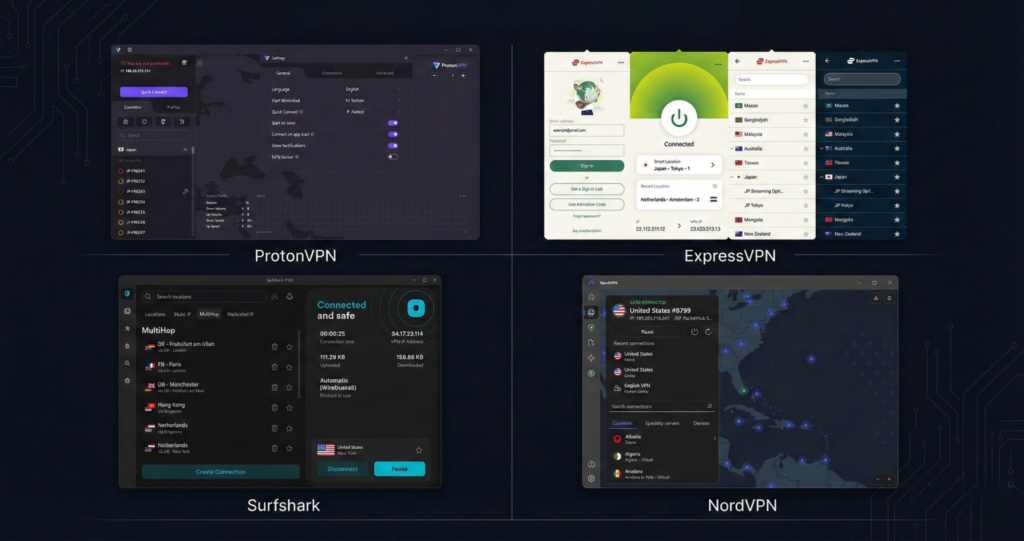
| Feature | NordVPN | Surfshark | ExpressVPN | Proton VPN |
|---|---|---|---|---|
| Kill switch | Yes | Yes | Yes | Yes |
| Split tunneling | Yes | Yes | Yes | Partial |
| Threat blocking | Threat Protection | CleanWeb | Threat Manager | Limited |
| Multi-hop routing | Yes | Yes | No | Secure Core |
| Unlimited devices | No | Yes | No | No |
| Open-source apps | No | No | No | Yes |
| Independent audits | Yes | Yes | Yes | Yes |
| Free plan | No | No | No | Yes |
| View Deal | View Deal | View Deal | View Deal |
Why this matters more in 2026
Cybersecurity analysts emphasize that automated attacks are increasing in scale and complexity, which means static protection methods struggle to keep up. Intelligent, adaptive defenses are becoming the new baseline rather than a premium feature.
5. Hidden Risks, Limitations & Ethical Concerns Most Sites Don’t Mention
AI-driven protection can improve security, but it also changes how decisions are made behind the scenes. Instead of fixed rules, some systems — including modern AI-powered VPNs — rely on automated models that analyze patterns and behavior to strengthen AI VPN security in real time.
Security researchers note that machine-learning security tools can sometimes produce false positives or false negatives if training data is incomplete or biased — meaning they may block safe activity or miss real threats. This is one of the reasons understanding how AI improves VPNs is important before relying on any system.
That doesn’t mean these tools are unsafe. It just means we should understand how they work, not treat them as magic — especially when choosing tools designed for real AI cybersecurity privacy.
Where risks can actually appear
| Risk Area | What Could Happen | How to Reduce Risk |
|---|---|---|
| Over-automation | System blocks legitimate traffic | Choose tools with manual override |
| Model bias | Incorrect threat detection | Providers with frequent updates |
| Transparency gaps | Unclear data handling | Audit-verified providers |
| False confidence | Users rely only on one tool | Layered security approach |
The ethical side of intelligent protection
There’s also a broader question:
If a system constantly analyzes traffic to detect threats, what data is it actually seeing when using tools like AI-powered VPNs?
Some privacy researchers point out that AI-driven security platforms must process behavioral signals to function effectively, which is why transparency and clear privacy policies are essential for real AI cybersecurity privacy and trustworthy AI VPN security.
That’s why reputable providers publish:
• independent audits
• data-handling disclosures
• security whitepapers
Without those, we’re essentially trusting a black box — and that’s not how VPN with AI protection should work.
What this means for us
The goal isn’t to avoid smart protection tools. It’s to use them wisely.
The safest approach is simple:
intelligent security + informed user = real protection
If you want to understand how hidden system design can influence digital behavior and trust, our analysis of dark design patterns in AI apps shows how subtle tech decisions can affect users without them noticing.
6. Final Verdict: Are AI-Powered VPNs Worth It in 2026? + FAQ

The internet is getting faster, smarter, and more convenient… but also more unpredictable. Logins get flagged, suspicious links appear, and sometimes things just don’t feel as safe as they used to. That instinct is actually useful. It’s our awareness catching up with how quickly technology is evolving.
So are AI-powered VPNs actually worth using?
Short answer: yes — but only when chosen carefully.
Quick verdict for different users
| User Type | Should You Use One? | Reason |
|---|---|---|
| Remote workers | Yes | Protects logins + work accounts |
| Frequent travelers | Yes | Public Wi-Fi risk protection |
| Casual users | Usually | Extra privacy layer |
| Privacy-focused users | Definitely | Real-time threat detection |
The honest conclusion
AI-powered VPNs aren’t magic shields. But they are a major step forward compared to traditional static protection.
Security researchers consistently emphasize that automated defenses are becoming essential because modern cyber threats move faster than manual response systems can react.
That’s the key difference:
Traditional protection reacts.
Smarter protection anticipates.
FAQ
Q: Are AI-powered VPNs safer than normal VPNs?
A: They can be, because some include real-time monitoring and adaptive protection instead of relying only on static encryption.
Q: Do AI VPNs track your activity?
A: Reputable providers don’t log identifiable data. Always choose services that publish independent audit reports to verify this.
Q: Are they worth paying for?
A: If you use public networks, work remotely, or manage important accounts, the extra protection layer is usually worth it.
Q: Is a VPN alone enough for security?
A: No. Security experts recommend layered protection — VPN + strong passwords + two-factor authentication.
Q: What’s the biggest mistake people make when choosing a VPN?
A: Trusting marketing claims instead of verifying transparency, audits, and security architecture.
Final Takeaways
AI isn’t replacing online privacy tools — it’s reshaping how they work. As threats become faster and more automated, protection has to evolve too. That’s why smarter security systems aren’t just a trend anymore; they’re becoming the new standard for staying safe online.
The key isn’t choosing the most advanced tool.
It’s choosing tools we understand and trust.
When we combine awareness, reliable technology, and good habits, privacy stops feeling complicated — and starts feeling manageable.
Want to go deeper into smart digital protection and AI-driven tools? These guides pair perfectly with what we covered here:

